Cloud Workload Security: What It Is and How to Get It Right

⚡ Quick Answer: What Is Cloud Workload Security? Cloud workload security is the practice of protecting the applications, services, virtual machines, containers, and data that run inside cloud environments. It covers security at the workload level – meaning not just the cloud infrastructure itself, but everything running on top of it. Under the cloud shared […]
IOC vs IOA: What’s the Difference and Why It Matters

⚡ Quick Answer: IOC vs IOA in 30 Seconds An Indicator of Compromise (IOC) is forensic evidence that a breach has already occurred – a digital fingerprint left after an attacker has been in your systems. An Indicator of Attack (IOA) is behavioural evidence that an attack is actively in progress – it detects what […]
NOC vs SOC: Key Differences Explained for Sydney Business Leaders (2026 Guide)
If you’re running a growing business in Sydney, you’ve likely heard the terms NOC and SOC thrown around during IT discussions. They sound similar. They both involve monitoring. And they both claim to protect your business. But they solve very different problems. Understanding the difference between a Network Operations Center (NOC) and a Security Operations […]
DNS and SSL Explained (2026): How They Protect Your Business Website
Every time someone visits your website, two invisible technologies go to work instantly: DNS and SSL. Most business owners never think about them — until something breaks. Misconfigured DNS can take your website offline. An expired SSL certificate can destroy trust overnight. And both directly impact your SEO rankings, security posture, and customer confidence. In […]
Romance Scams & Red Flags: This Valentine’s Day, Protect Your Heart and Your Data

Love is in the air… and so are cybercriminals.Valentine’s Day is a time to connect, celebrate relationships, and express affection. But it’s also a peak season for online scams—especially romance scams that target people through dating apps, social media, and emails. At Code Hyper One, we want to remind individuals and businesses alike: emotions can […]
Building a Security Operations Center (SOC) in 2026: What Businesses Need to Know

Why Building a SOC Is No Longer Optional Cyber attacks no longer announce themselves. They hide inside legitimate traffic, abuse trusted user accounts, and quietly move laterally across networks. This shift is exactly why building a Security Operations Centre (SOC) has become a business requirement rather than a technical luxury. A SOC exists to provide […]
Cyber Risk Management Framework for Australian Businesses (2026 Guide)

Cyber threats are no longer hypothetical. For Australian businesses, cyber risk is now an operational, financial, and legal concern—not just an IT issue. A structured cyber risk management framework helps businesses identify threats, reduce exposure, and respond effectively when incidents occur. Without one, security decisions become reactive, inconsistent, and dangerously incomplete. This guide explains what […]
Disaster Recovery Plan Checklist for Businesses (2026)

Unexpected IT disruptions can bring business operations to a standstill. Cyberattacks, system failures, cloud outages, and human error can all result in lost data, prolonged downtime, and serious financial impact. A disaster recovery plan checklist helps businesses prepare for these scenarios before they happen. Instead of reacting under pressure, organisations follow a clear recovery framework […]
Stop Fake Emails: Email Spoofing Prevention for Businesses

Email spoofing is when an attacker forges the From: address so messages look like they come from someone you trust, a supplier, a bank, or a colleague. For businesses, a single spoofed email can cause data loss, financial fraud, or reputational damage. This article explains email spoofing prevention in plain language and gives you a […]
Cyber Risk Management: Protect Your Business

What this guide will do for you If you run a business today, cyber risks are business risks. This guide to cyber risk management gives you a practical, commercial playbook: how to identify your highest-impact cyber risks, assess and prioritise them, build a defensible security risk management plan, and use managed IT services to reduce […]
The Hidden Dangers of Public Wi-Fi & How Cloud Security Helps

Public Wi-Fi has become a modern convenience we rarely think twice about. Whether it’s at a café, airport, hotel, or shopping centre, connecting to free Wi-Fi is part of everyday life for Australians. But while public Wi-Fi keeps you connected on the go, it also opens the door to significant cybersecurity risks—especially for businesses. In […]
Responding to Alerts in EDR: Why It’s Critical, Not Optional
In today’s cybersecurity landscape, ignoring alerts is one of the biggest mistakes businesses can make. With Endpoint Detection and Response (EDR) solutions, security teams receive real-time alerts about suspicious activities, malware, or system anomalies. However, simply receiving an alert isn’t enough—how you respond determines whether your business stays protected or falls victim to an attack. […]
How Staged Cyber Attacks Work: A Step-by-Step Breakdown
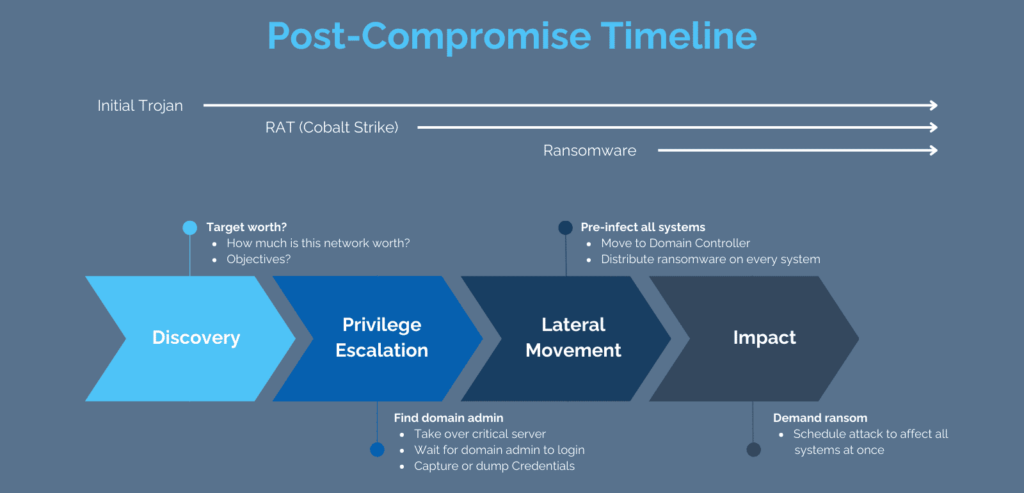
Cybercriminals don’t just attack at once—they use staged cyberattacks to infiltrate, escalate, and detonate malware inside a target network. These attacks are highly strategic, allowing hackers to evade detection, steal credentials, and cause maximum damage. At Code Hyper One, we help businesses understand, detect, and prevent staged cyberattacks before they can wreak havoc. Let’s break […]
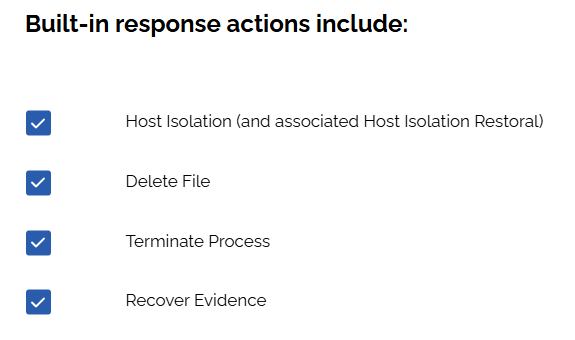
EDR Eradication: Eliminating Cyber Threats with Precision
Endpoint Detection and Response (EDR) is a critical component of modern cybersecurity, designed to detect, investigate, and respond to cyber threats in real-time. One of the most crucial phases of EDR is Eradication, where security teams ensure that identified threats are completely removed from affected systems. At Code Hyper One, we help businesses implement effective […]
The Role of Disaster Recovery in Cybersecurity

In today’s digital world, businesses face constant threats from cyberattacks, data breaches, and system failures. A single cyberattack can cripple operations, leak sensitive data, and cause financial loss. That’s why organisations must have a strong disaster recovery (DR) plan as part of their overall cybersecurity strategy. Disaster recovery plays a critical role in minimising damage and ensuring […]
The Future of Cybersecurity: Integrating AI into Phishing Simulations

As cyber threats grow more sophisticated, businesses are increasingly focusing on improving their defense systems. One of the most common and dangerous threats is phishing, where attackers trick individuals into revealing sensitive information by posing as trustworthy sources. Phishing simulations have become a key tool in training employees to recognise phishing attempts, but now, a […]
Mastering Incident Response: A Step-by-Step Guide to Cybersecurity Resilience

Cyber threats are evolving at an alarming rate, making it critical for businesses to have a solid incident response plan in place. The NIST Cybersecurity Framework outlines a 4-step Incident Response Process that helps organisations detect, contain, and recover from cyberattacks efficiently. At Code Hyper One, we specialise in proactive cybersecurity solutions that help businesses […]
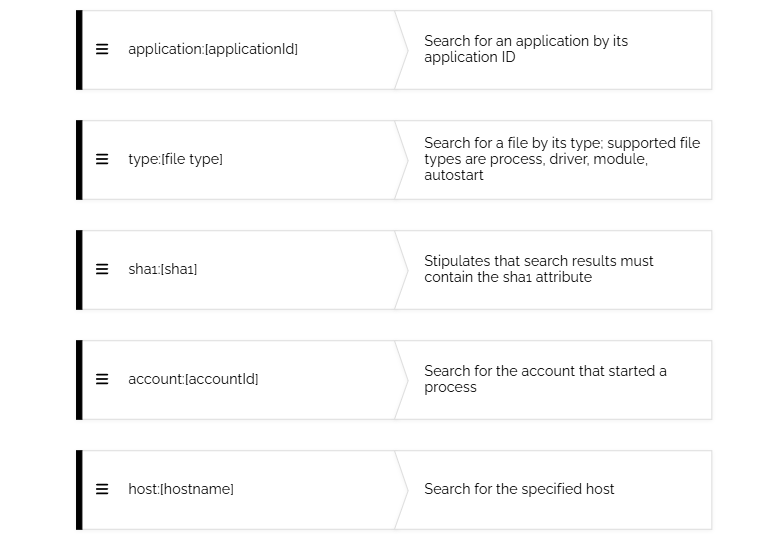
Malware Alerts vs Behavioral Alerts in EDR: Understanding the Difference
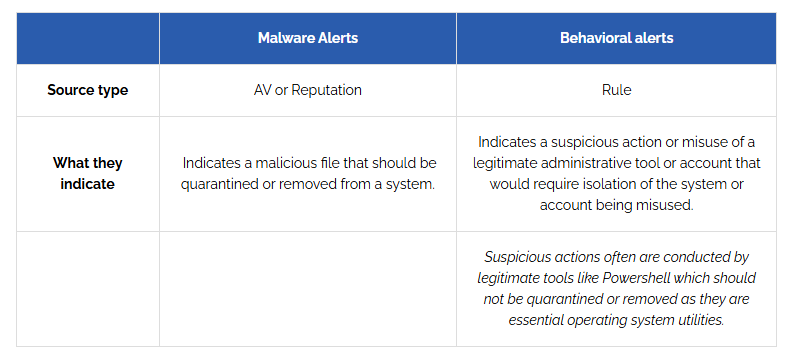
Cybersecurity threats are evolving, making Endpoint Detection and Response (EDR) a crucial tool for businesses. One of the key components of EDR is alerting, which helps security teams identify potential threats before they escalate. However, not all alerts are the same—there are Malware Alerts and Behavioral Alerts, and understanding the difference is critical to effective […]
Top Cloud Migration Benefits: Cost Savings and Flexibility

Cloud migration has become a game-changer for businesses worldwide. In fact, over 90% of organisations have already adopted some form of cloud technology to streamline operations, enhance security, and reduce costs. The cloud offers numerous benefits, including flexibility, scalability, and access to advanced technologies, making it an essential tool for companies aiming to stay competitive in […]
Let Your Heart Be Stolen, But Not Your Precious Data! ❤️🔒

Love is in the air! 💕 Valentine’s Day is all about trust, connection, and deep bonds—just like the relationship you should have with your cybersecurity. While you’re busy planning the perfect romantic evening, cybercriminals are plotting their own kind of romance scams, phishing attacks, and data breaches. At Code Hyper One, we believe that while […]
What Is VoIP Technology? Learn How This Technology Transforms Calling

VoIP technology (Voice over Internet Protocol) is a system that allows voice calls to be made over the internet instead of traditional phone lines. It converts voice signals into digital data and transmits them online, enabling users to make calls from computers, smartphones, or VoIP-enabled devices. VoIP is widely used for its cost savings, flexibility, […]
How AI in Everyday Life is Quietly Reshaping Cybersecurity

Artificial Intelligence (AI) is no longer a futuristic concept—it’s part of our everyday lives. From voice assistants like Alexa and Siri to self-driving cars and personalized recommendations on Netflix and Spotify, AI is revolutionising how we interact with the world. However, as AI becomes more embedded in our daily routines, it brings along a host […]
What Is Email Security Gateway? How It Protects Your Business Inbox

An email security gateway is a tool that protects your inbox from unwanted or harmful emails. It works by filtering out spam, viruses, phishing attempts, and other malicious content before they reach your inbox. This helps ensure that your email communications remain safe and secure. Why is Email Security Important? Protects personal data: Keeps sensitive […]
9 Types of Vulnerability Scan Network to Protect Your System

Keeping your network safe from cyber threats is like locking the doors to your house. A vulnerability scan network helps you find weak spots in your system before hackers do. Think of it as a digital security check-up that keeps your data and devices protected. But did you know there are different types of vulnerability […]
Why Entra ID Protection is Key to Online Security

Importance of Entra ID Protection Entra ID Protection is critical for ensuring identity security and maintaining trust in the digital space. Here’s why it matters: Prevents Unauthorized Access: Blocks suspicious login attempts to protect sensitive accounts. Detects Security Threats: Identifies unusual activity to mitigate risks early. Secures Sensitive Data: Ensures personal and business information stays […]
Lessons from the PM Anthony Albanese Impersonating AI Scam

AI scams like the recent Hon Anthony Albanese impersonation remind us of the need for vigilance. Learn how to identify and protect yourself from AI-driven manipulation.
Why Do You Need a Smart Door Lock?

Installing a smart door lock is just one step toward stronger security at home—and your business needs a similar multi-layered approach. Learn why layered cybersecurity is essential for small businesses today.
Why RMM is important?

With an RMM solution, you can proactively monitor and maintain all your systems, ensuring security, efficiency, and scalability.
