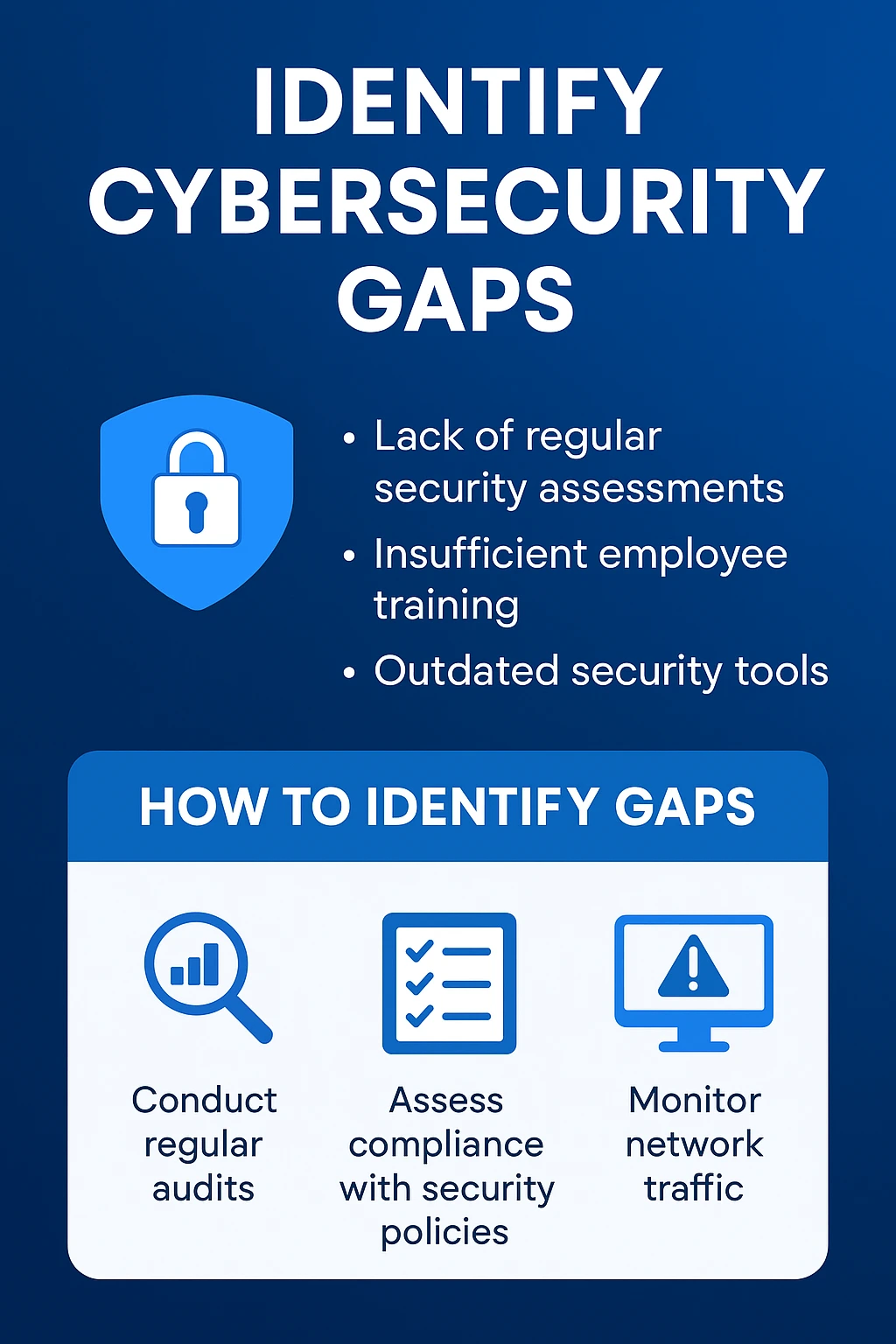
Cybersecurity gaps: what they are, why they matter, and how to close them
If your business hasn’t had a recent security check, you almost certainly have cybersecurity gaps, weaknesses that attackers can turn into breaches, downtime, or data loss. This article explains the most common cybersecurity gaps, their real business impact, and practical steps (including when to call experts) to close them. You’ll get an actionable gap-analysis mindset and clear links to the services that can remediate each issue.
Throughout this guide we use the phrase cybersecurity gaps to mean any missing control, process, or configuration that increases risk, from unpatched systems and weak email security to insufficient backup or monitoring.
Why “cybersecurity gaps” is a commercial search intent, and why that matters
Searchers for “cybersecurity gaps” are typically in the problem/solution discovery phase: they know something’s wrong (or want to be proactive) and are evaluating whether to fix it in-house or hire a provider. That makes this content ideal for convincing readers that remediation is urgent and that a managed IT/security partner can deliver measurable value.
If your business uses managed services, this is the perfect place to show:
- how gaps map to real services (e.g., patching → RMM; monitoring → SOC/MDR), and
- how those services reduce risk, downtime, and compliance headaches.
The top 9 cybersecurity gaps every business should check
Below are the gaps we see most often, they’re quick to find, costly if ignored, and easy to prioritise.
- Lack of multi-factor authentication (MFA) — One stolen password becomes a full break-in.
- Unpatched or end-of-life software — Known vulnerabilities remain exploitable.
- No regular backups or untested recovery — Ransomware or hardware failure becomes catastrophic.
- No continuous monitoring / limited detection — Attacks can dwell undetected for months.
- Inadequate email security and phishing awareness — Humans are the most common attack vector.
- Weak access control & excessive privileges — Too many users have broad access they don’t need.
- Outdated endpoint protection / missing EDR — Endpoint compromise spreads laterally.
- No formal incident response plan — When things go wrong, recovery is chaotic and slow.
- Poor network segmentation & misconfigured devices — Lateral movement and data exfiltration are easier.
Many of these are highlighted in the Australian Cyber Security Centre’s small business guidance and reflect the NIST framework’s recommendations for identifying and prioritising gaps. See practical guidance from the ACSC and NIST for small businesses.
ACSC small business guidance
NIST Cybersecurity Framework resources
Quick comparison: common gaps, business impact, and fixes
Cybersecurity gap | Typical business impact | Recommended mitigation | Code Hyper One service to consider |
No MFA | Account takeovers, data breaches | Enforce MFA (conditional access) | Microsoft 365 hardening / Identity (link to Microsoft identity services) |
Unpatched systems | Exploits, ransomware | Centralised patch management | Remote monitoring & management (RMM) / patching |
Missing backups | Data loss, prolonged downtime | Regular, encrypted backups + test restores | |
No EDR | Undetected malware, lateral spread | Deploy EDR with automated response | |
Limited monitoring | Late breach detection | 24/7 SOC / MDR | |
Phishing vulnerability | Credential theft, fraud | Phishing simulation + email filtering | |
Poor segmentation | Broad blast radius for attacks | Network segmentation & firewall rules |
How to run a quick internal gap analysis (non-technical checklist)
You don’t need a 100-page audit to spot the big risks. Use this high-level checklist to triage:
- Are all user accounts protected by MFA? (Yes/No)
- Are critical systems still on end-of-life OS? (Yes/No)
- When was the last successful restore test from backup? (Date)
- Are logs centrally collected and reviewed daily? (Yes/No)
- Is email filtered for phishing and malicious attachments? (Yes/No)
- Do your remote workers use company-managed devices with EDR? (Yes/No)
- Is there an incident response plan and a named responder? (Yes/No)
Any “No” is a priority. Start with MFA, backups and patching — they provide the largest risk reduction per dollar.
Prioritising gaps: risk, reach, and recoverability
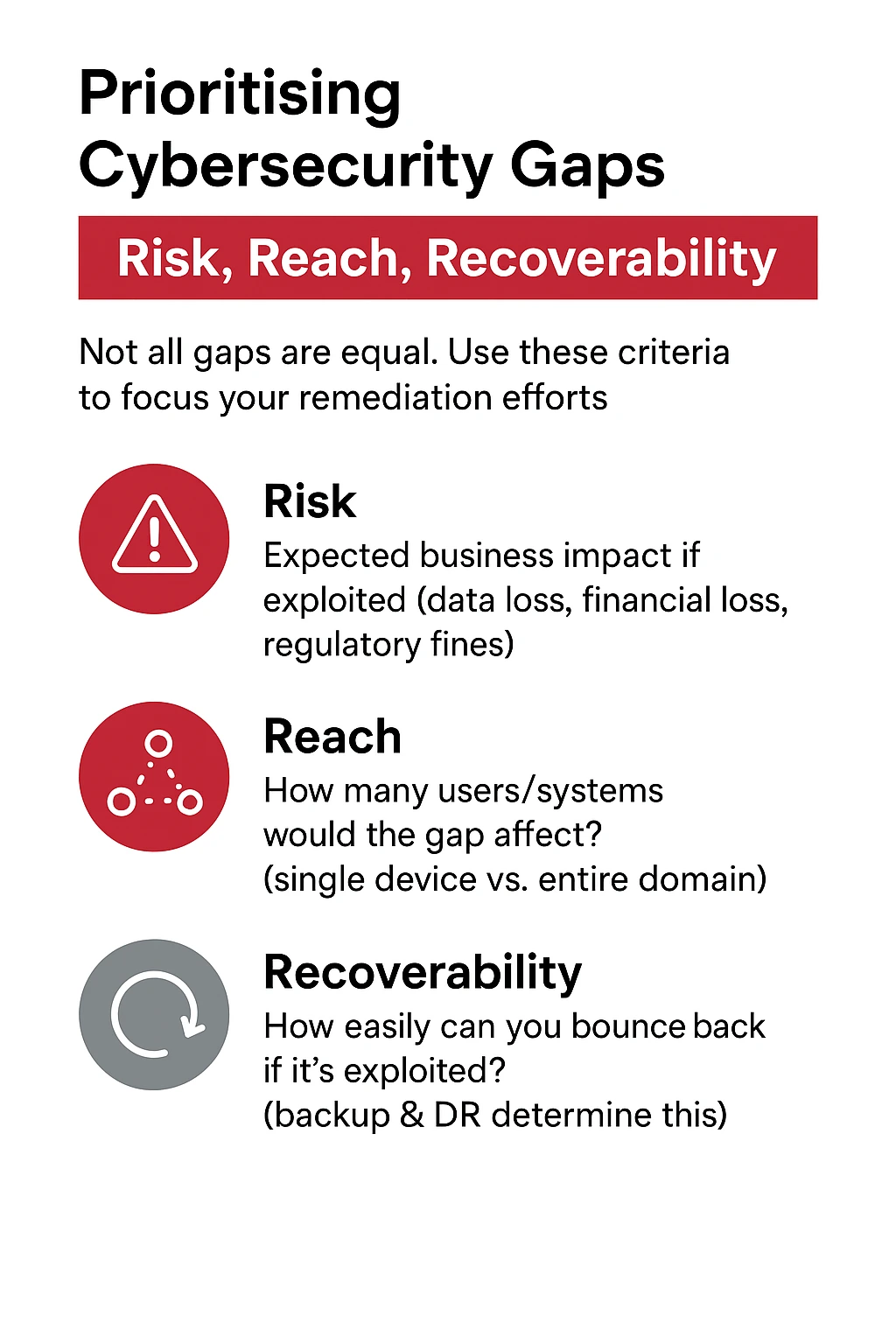
Not all gaps are equal. Use three lenses to prioritise remediation:
- Risk — What is the expected business impact if exploited? (data loss, financial loss, regulatory fines)
- Reach — How many users/systems would the gap affect? (single device vs. entire domain)
- Recoverability — How easily can you bounce back if it’s exploited? (backup & DR determine this)
Fix high-risk, high-reach, low-recoverability gaps first (e.g., backups before cosmetic security UI changes).
Tactical fixes you can implement this week
If you want immediate improvements, these are fast wins:
- Turn on MFA for all admins and high-risk accounts.
- Enable automated OS and app patching via RMM.
- Schedule daily encrypted backups and run a restore test.
- Deploy EDR on endpoints and enable alerts.
- Implement a basic phishing simulation and short awareness session.
- Harden email: SPF, DKIM, DMARC + inbound filtering.
- Limit admin privileges using least-privilege principles.
If any of those steps are unfamiliar, Code Hyper One can implement them end-to-end: from patching and backups to EDR and SOC monitoring. See how network security and penetration testing map to these fixes on the Code Hyper One pages: network security services and penetration testing.
When to bring in a managed IT/security partner
Hire external help when:
- You lack staff with hands-on security or SOC experience.
- The business can’t tolerate long downtime (healthcare, finance, legal).
- You need rapid remediation after an incident.
- Regulatory/compliance requirements demand formal controls.
- You want a continuous, proactive approach (24/7 monitoring, vulnerability management).
A managed partner provides not just tooling but people and processes — continuous vulnerability scanning, scheduled penetration tests, SOC monitoring, and tested BCDR — that prevent gaps from reappearing.
For example, Code Hyper One bundles continuous vulnerability scanning, penetration testing, EDR and SOC/MDR into a managed stack that closes and monitors gaps across the estate. See their vulnerability scanning and penetration testing pages for details.
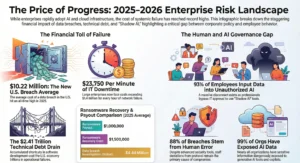
Cost vs. consequence: ROI on closing gaps
Fixing gaps is an investment. Compare the immediate cost of remediation against the potential cost of a breach:
- Average cost of a small-business cyber incident in Australia can reach tens of thousands of dollars (lost revenue, recovery, fines, reputational damage).
- A managed backup + monitoring stack often costs a fraction of potential loss while dramatically improving recovery time and reducing breach likelihood.
Use a free risk review or gap assessment (many managed providers offer one) to quantify ROI for your environment.
E-E-A-T: experience and trust signals to include on pages about gaps
When you publish content or a service page about closing cybersecurity gaps, demonstrate E-E-A-T by:
- Describing real, anonymised examples of gaps you fixed.
- Sharing measurable outcomes (recovery time, cost saved).
- Citing authoritative sources (ACSC, NIST) for recommended controls.
- Explaining frameworks used (NIST CSF gap analysis, AZURE/M365 best practices).
For small business guidance, see the ACSC small business hub and NIST Cybersecurity Framework materials linked earlier.
Conclusion: turn gaps into a predictable security posture
Cybersecurity gaps are normal; what matters is how quickly you find and fix them. Start with high-impact controls (MFA, patching, backups, EDR, monitoring), prioritise by risk and reach, and create a habit of continuous assessment. If you lack the time or skills, a managed provider can implement, monitor and maintain these controls so you can focus on your core business.
If you’d like, a free security review will identify your top 3-5 gaps and recommend a remediation roadmap tailored to your environment.
Frequently Asked Questions
What exactly counts as a cybersecurity gap?
A cybersecurity gap is any missing or ineffective control, configuration, process, or policy that raises your organisation’s cyber risk, for example, an unpatched server, accounts without MFA, or backups that haven’t been tested.
How long does it take to fix common gaps like MFA and patching?
Turning on MFA for users can be done in hours (plus user onboarding). Centralised patching via an RMM can be configured in days and then runs automatically. More complex fixes (network segmentation, SOC deployment) can take weeks, depending on scale.
Can a small business afford to implement continuous monitoring or SOC services?
Yes, modern managed SOC/MDR offerings are modular and scalable. They provide enterprise-grade monitoring at a small-business price point relative to the cost of a breach. If you want to explore options, a managed provider can propose a phased approach.
How do frameworks like NIST or ACSC help with gap analysis?
Frameworks offer structured ways to assess current controls, define a target posture, and prioritise gaps by business impact and feasibility. Use them to translate technical gaps into business priorities. See NIST’s guidance for small organisations and the ACSC small business resources.