✍️ About This Guide Written by the cybersecurity advisory team at CodeHyper, a Sydney-based managed IT and cybersecurity provider. Our team has conducted Essential Eight gap assessments and maturity uplifts for Australian businesses across professional services, healthcare, construction, and financial services. Statistics in this guide are sourced from the ASD Annual Cyber Threat Report 2023–24, the ACSC Annual Cyber Threat Report, and the official Essential Eight Maturity Model published at cyber.gov.au. This guide reflects ASD’s most current published guidance as of March 2026. |
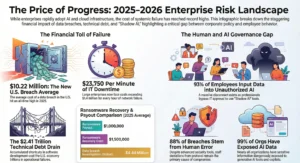
In the 2023–24 financial year, the Australian Signals Directorate received 87,400 cybercrime reports — roughly one every six minutes. The average cost of a cybercrime incident to a small Australian business now exceeds $50,000 AUD, and for larger businesses the figure surpasses $100,000. Yet the majority of these incidents exploited vulnerabilities that a well-implemented set of eight security controls could have prevented entirely.
Those eight controls are the ASD Essential Eight — Australia’s most authoritative cybersecurity baseline, developed and maintained by the Australian Signals Directorate (ASD). Originally designed for Commonwealth government agencies, the Essential Eight is now the de facto security standard for Australian organisations across every sector: private businesses, healthcare providers, professional services firms, financial institutions, and anyone that holds sensitive data or does business with government.
In 2026, the pressure to comply has never been higher. Cyber insurers are requiring proof of Essential Eight maturity before issuing or renewing policies. Government procurement increasingly mandates it. And with the ASD signalling that Maturity Level Two is now the expected baseline for mid-sized businesses — not the aspirational goal — the window for treating the Essential Eight as optional has closed.
This guide covers everything you need to know: what the ASD Essential Eight is, each of the eight controls explained in plain English, the four maturity levels, what has changed in 2026, a real case study, and a practical roadmap to get started. For hands-on implementation support, explore our managed cybersecurity services or read our companion Essential Eight checklist for 2025.
What Is the ASD Essential Eight?
The ASD Essential Eight is a set of eight prioritised cybersecurity mitigation strategies developed by the Australian Signals Directorate (ASD) through its operational arm, the Australian Cyber Security Centre (ACSC). First published in June 2017 as an evolution of the original ‘Top 4’ mandatory controls, the Essential Eight represents the minimum security baseline ASD recommends for all Australian organisations operating internet-connected IT systems.
The framework is built on a foundational insight from ASD’s threat intelligence and incident response work: the vast majority of cyberattacks exploit a small, well-understood set of weaknesses. Over 85% of successful intrusions could have been prevented by implementing just the first four controls — and the full eight address a comprehensive range of attack vectors used by both opportunistic and sophisticated adversaries.
The eight strategies are grouped across three objectives:
- Objective 1 – Prevent Attacks: Application Control, Patch Applications, Configure Microsoft Office Macro Settings, User Application Hardening
- Objective 2 – Limit the Extent of Incidents: Restrict Administrative Privileges, Patch Operating Systems, Multi-Factor Authentication
- Objective 3 – Recover Data and System Availability: Regular Backups
Critically, the Essential Eight is not a product you can purchase or a certification you complete once. It is an ongoing operational discipline — a framework of controls that must be implemented, maintained, tested, and continuously improved as the threat landscape evolves. ASD updates the Essential Eight Maturity Model regularly to reflect new attacker techniques observed through its cyber threat intelligence and incident response activities.
ASD Essential Eight vs ACSC Essential Eight: Are They the Same?
Yes. The terms are interchangeable. The Australian Cyber Security Centre (ACSC) is a division of the Australian Signals Directorate (ASD). The framework is published on the official cyber.gov.au website and is often referred to as either the ‘ASD Essential Eight’ or the ‘ACSC Essential Eight’ — both refer to the same framework. You may also see it written as ‘Essential 8’, ‘E8’, or ‘ASD E8’.
The ASD Essential Eight Controls Explained
Here is a plain-English breakdown of each control, what it means in practice, why it matters, and what implementing it looks like for a typical Australian business.
Control 1: Application Control
What it is: Only approved, trusted applications are permitted to execute on your endpoints and servers. Everything else — unauthorised software, malicious executables, unapproved scripts — is blocked by default.
Why it matters: Ransomware, malware, and attacker tools are all ‘applications’. If your systems only allow approved software to run, malicious code cannot execute — even if it lands on your machine through a phishing email or drive-by download.
In practice: Use Microsoft Intune with Windows Defender Application Control (WDAC) or AppLocker to create and enforce allowlists on all workstations and internet-facing servers. Microsoft’s recommended block rules must also be implemented. Rulesets should be validated at least annually.
Common gap: Organisations often implement application control on workstations but leave servers unenforced — a critical gap since servers are high-value targets.
Control 2: Patch Applications
What it is: Internet-facing applications and all software on endpoints must be patched within defined timeframes after vendors release security updates.
Why it matters: ASD data shows that 1 in 5 vulnerabilities are exploited within 48 hours of a patch being released. Unpatched applications — particularly browsers, PDF readers, Microsoft Office, and internet-facing web applications — are among the most exploited attack vectors in Australia.
In practice: At Maturity Level One, patching within 30 days is required. Maturity Level Two requires patching within 14 days — and within 48 hours for vulnerabilities with existing exploits. Maturity Level Three mandates patching within 48 hours across the board, with automated discovery and deployment tooling. Applications that are no longer supported by vendors and cannot be patched must be removed.
Common gap: Businesses patch Microsoft products regularly but neglect third-party applications like Adobe Acrobat, 7-Zip, VLC, and browser plugins. Attackers specifically target these ‘forgotten’ applications.
Control 3: Configure Microsoft Office Macro Settings
What it is: Microsoft Office macros — scripts embedded in Word, Excel, and PowerPoint documents that can execute code — must be disabled for users who don’t need them and restricted to digitally signed macros from trusted publishers for those who do.
Why it matters: Macros embedded in email attachments remain one of the most common malware delivery mechanisms in Australia. Business email compromise and phishing campaigns routinely use macro-enabled documents to execute initial payloads. Without macro controls, a single click on a malicious attachment can give an attacker full system access.
In practice: Use Microsoft Intune or Group Policy to enforce macro settings organisation-wide. At higher maturity levels, only macros digitally signed by a certificate from a trusted internal publisher are permitted to run. Logging of blocked macro execution events is required from Maturity Level Two.
Control 4: User Application Hardening
What it is: Configure user-facing applications — particularly web browsers — to reduce their attack surface by disabling unnecessary features, blocking dangerous content, and preventing exploitation of built-in application capabilities.
Why it matters: Web browsers are the most common attack entry point for end users. Browser-based attacks — malicious scripts, drive-by downloads, browser plugin exploitation — are extremely common and highly effective against unprotected browsers.
In practice: Disable Internet Explorer (deprecated), block web advertisements using browser policy (advertisements are a common malware delivery vector), disable Java in browsers, configure PowerShell in Constrained Language Mode, and block web content categories that are known malware delivery channels. Ensure all supported browser versions are enforced via policy.
Control 5: Restrict Administrative Privileges
What it is: Administrative access — the ability to make system-wide changes — is granted only to users who explicitly require it for their role, using dedicated privileged accounts separate from their day-to-day accounts. Privileged access is actively managed, reviewed, and revoked when no longer required.
Why it matters: This is the control that limits how far an attacker can move after they gain an initial foothold. If every user is an administrator, a single compromised account gives an attacker god-mode access across the environment. Restricting privileges means a compromised standard user account has minimal damage potential.
In practice: Remove local administrator rights from all standard users. Create separate privileged accounts for IT staff that are used exclusively for administrative tasks. Implement Privileged Identity Management (PIM) through Microsoft Entra ID to provide just-in-time privileged access with approval workflows. Disable privileged accounts after 45 days of inactivity. At Maturity Level Three, privileged users must operate from separate privileged environments and administrative activities should be conducted through jump servers.
Common gap: This is the most frequently failed control in Australian SMB assessments. Widespread local admin rights — often granted historically for convenience — are the single biggest predictor of a catastrophic breach outcome.
Control 6: Patch Operating Systems
What it is: Operating system vulnerabilities on workstations, servers, and network devices must be patched within defined timeframes, and operating systems that no longer receive security updates from vendors must be replaced.
Why it matters: Operating system vulnerabilities are exploited to escalate privileges, establish persistence, and move laterally. The WannaCry ransomware attack — which caused billions in global damage — exploited a Windows OS vulnerability for which a patch had been available for months. Unpatched operating systems are the backbone of most sophisticated attacks.
In practice: Use Windows Update for Business, Microsoft Intune, or an RMM platform to centrally manage and enforce OS patching across all endpoints and servers. At Maturity Level Two, internet-facing servers must be patched within 48 hours of an actively exploited vulnerability being disclosed. End-of-life operating systems — including Windows 10, which reaches end of support in October 2025 — must be replaced or isolated.
Control 7: Multi-Factor Authentication (MFA)
What it is: Users must verify their identity using two or more factors — something they know (password) plus something they have (authentication app, hardware token) or something they are (biometric) — before accessing systems, especially internet-facing services and privileged accounts.
Why it matters: Password theft is involved in the majority of successful breaches in Australia. Credentials are stolen through phishing, credential stuffing, and data breach exposure. MFA breaks the attack chain: even if an attacker has a user’s password, they cannot authenticate without the second factor.
In practice: Enforce MFA for all users accessing cloud services, remote access, and administrative systems. From Maturity Level Two, phishing-resistant MFA is required for privileged users — this means hardware security keys (FIDO2) or certificate-based authentication, not SMS OTPs which can be intercepted through SIM-swapping. Microsoft Entra ID with Conditional Access policies provides the technical foundation for Essential Eight MFA compliance across Microsoft 365 and Azure environments.
2026 update: ASD is pushing strongly for phishing-resistant MFA adoption across all maturity levels, not just privileged users. The Medibank breach — in which attackers accessed internal systems using stolen credentials without MFA — was a direct catalyst for this tightening.
Control 8: Regular Backups
What it is: Important data, software, and configuration settings must be backed up regularly, with backups stored securely, tested periodically, and retained in a manner that allows recovery even if primary systems — including the backup infrastructure itself — are compromised.
Why it matters: Ransomware groups specifically target backup systems first because destroying your backups eliminates your recovery options and maximises their leverage. Without verified, isolated backups, a ransomware incident leaves you with two choices: pay the ransom or rebuild from scratch — both of which are enormously expensive.
In practice: Follow the 3-2-1 backup rule: three copies of data, on two different media types, with one copy stored offsite and offline (or immutable). Backups must be tested at least quarterly — a backup you’ve never tested is not a backup. At Maturity Level Three, backups must be completely isolated from production networks and protected against modification and deletion. Services like Microsoft 365 backup and OneDrive backup configuration are essential components of an Essential Eight-compliant backup strategy for Microsoft environments.
The Essential Eight Maturity Model: Understanding Levels 0 to 3
The ASD Essential Eight Maturity Model defines four maturity levels — Level 0 through Level 3 — that represent progressively more robust implementation of each control. ASD recommends that organisations achieve the same maturity level across all eight controls before advancing — implementing a patchwork of high maturity in some controls and low maturity in others leaves exploitable gaps.
Maturity Level | Protection Against | Requirements Summary | Suited For |
Level 0 – Unprepared | Nothing — significant exposure to all common threats | Controls are absent, incomplete, or not functioning as intended | No organisation should remain at Level 0 |
Level 1 – Basic | Opportunistic attacks using commodity tools and automated techniques | Fundamental implementation of each control with manual processes acceptable | Starting point for small businesses and those new to the framework |
Level 2 – Intermediate | Adversaries investing moderate effort with standard tradecraft | More comprehensive implementation; some automation required; phishing-resistant MFA for privileged users | Mandatory for Commonwealth entities; recommended baseline for Australian businesses with sensitive data |
Level 3 – Advanced | Sophisticated adversaries with significant resources, time, and advanced techniques | Fully automated, monitored, and continuously tested controls; privileged access isolation; immutable backups; FIDO2 MFA universal | Critical infrastructure, government agencies, businesses in high-threat environments |
In 2026, ASD’s position has solidified: Maturity Level Two is the expected baseline for mid-sized Australian businesses, service providers, and any organisation handling sensitive customer data. Maturity Level One is appropriate only as a starting point — not a destination. For government-connected businesses, Level Two is effectively mandatory.
ASD’s guidance also emphasises a critical implementation principle: balance your maturity across all eight controls. An organisation at Level 3 for MFA but Level 0 for Application Control is not at Level 3 — it’s at Level 0. Attackers will find and exploit the weakest control. Your overall maturity is only as strong as your lowest-performing control.
What’s Changed in 2026: ASD Essential Eight Updates You Need to Know
The ASD Essential Eight is a living framework, updated regularly as attacker techniques evolve. Here are the most significant changes and emphasis shifts shaping Essential Eight compliance in 2026.
1. Phishing-Resistant MFA Is No Longer Optional for Privileged Users
SMS-based one-time passwords (OTPs) are no longer considered phishing-resistant MFA under the Essential Eight. ASD has clarified that from Maturity Level Two, privileged users must use FIDO2 hardware security keys or certificate-based authentication. This change was driven by the increasing prevalence of real-time phishing proxies (tools like Evilginx) that can intercept SMS OTPs and session tokens in transit — a technique used in several high-profile Australian breaches.
2. Patch Timelines Are Tightening
ASD has increased urgency around patching for actively exploited vulnerabilities. The expectation at Maturity Level Two is patching within 48 hours when exploitation exists in the wild — not 14 days. This requires automated patch deployment tooling rather than manual IT processes. Organisations relying on monthly patch windows are non-compliant at Level Two for any vulnerability with a live exploit.
3. Cloud and Identity Controls Are Under Greater Scrutiny
With Australian businesses increasingly built on Microsoft 365, Azure, and SaaS platforms, ASD has sharpened its guidance around cloud identity, conditional access, and third-party risk. The Medibank and Latitude breaches — both involving compromised credentials and insufficient identity controls — have accelerated ASD’s push for stronger identity architecture including Conditional Access policies, just-in-time privileged access, and user account lifecycle management.
4. Backup Isolation and Testing Requirements Are Stricter
ASD now explicitly requires that backups at higher maturity levels be isolated from the production environment and protected against modification and deletion — i.e., immutable backups. Additionally, restoration testing must be documented. A backup strategy that has never been tested is treated as non-compliant, because an untested backup is operationally equivalent to no backup.
5. Logging and Monitoring Fidelity Is Increasing
From Maturity Level Two, centralised logging of security events — particularly privileged access events, application control events, and authentication events — is required. ASD is signalling that organisations need Security Information and Event Management (SIEM) or equivalent capabilities to aggregate, analyse, and alert on security events in a timely manner. Our article on building a Security Operations Centre explains how to approach this for Australian SMBs.
Why the ASD Essential Eight Matters for Australian SMBs — Not Just Government
A common misconception is that the Essential Eight is a government compliance framework with limited relevance to private businesses. This was arguably true in 2017. It is definitively untrue in 2026. Here is why every Australian business needs to take the Essential Eight seriously.
Cyber Insurance Is Requiring It
Australian cyber insurance underwriters now routinely assess Essential Eight maturity during policy applications and renewals. Businesses that cannot demonstrate at least Maturity Level One — and increasingly Level Two — face higher premiums, reduced coverage limits, or outright policy refusal. This makes the Essential Eight a financial imperative, not just a security one.
Government Contracts Are Mandating It
If your business provides services to any Australian government agency — federal, state, or local — you are increasingly expected to demonstrate Essential Eight compliance as a condition of contract. The PSPF (Protective Security Policy Framework) mandates it for Commonwealth entities, and supply chain requirements are cascading this obligation to government suppliers and contractors.
Attackers Specifically Target Gaps in These Controls
Cybercriminals and ransomware groups actively scan for organisations that haven’t implemented the Essential Eight. Tools that identify unpatched systems, organisations without MFA, and environments with excessive admin rights are widely available in attacker toolkits. The Essential Eight controls were specifically chosen because they address the most commonly exploited weaknesses — which means failing to implement them is not theoretical risk management. It is a known, concrete vulnerability.
The Cost of Non-Compliance Exceeds the Cost of Implementation
The average cost of a cybercrime incident for a small Australian business exceeds $50,000 — and that excludes reputational damage, regulatory consequences under the Privacy Act, and the operational disruption of a ransomware recovery. A full Essential Eight implementation for an SMB typically costs a fraction of that. The ROI of Essential Eight compliance is not ambiguous — it is one of the clearest investments in risk reduction available to Australian businesses. Our managed cybersecurity services are designed specifically to deliver Essential Eight maturity uplift at a cost that makes financial sense for SMBs.
�� Real-World Case Study: From Maturity Level 0 to Level 2 in 12 Weeks — A Melbourne Construction Business
Case Study Snapshot Industry: Construction & Project Management | Location: Melbourne, VIC | Staff: 85 | Cloud Platform: Microsoft 365 + on-premises Windows Server | Starting Maturity: Level 0 across all eight controls | Outcome: Maturity Level 2 achieved in 12 weeks | Trigger: Failed cyber insurance renewal due to inadequate security posture |
The Situation
A Melbourne-based construction and project management business with 85 staff contacted CodeHyper in late 2024 after their cyber insurance broker informed them at renewal that their existing policy would not be renewed unless they could demonstrate meaningful cybersecurity improvement. The broker had provided a checklist that mapped directly to Essential Eight Maturity Level Two requirements.
An initial gap assessment found the business at Maturity Level 0 across all eight controls. The specific findings were not surprising for an SMB of this size and profile — they were emblematic of the national picture:
- Application Control: No allowlisting in place. Users had local admin rights and could install any software without approval. Multiple unlicensed and unvetted applications were found running across the environment
- Patch Applications: Patch management was performed manually by a part-time IT contractor. Seven endpoints had not received application patches in over 60 days. Three internet-facing applications were running versions with known critical vulnerabilities
- Office Macro Settings: Macros were enabled by default for all users with no restrictions. Two staff members regularly received and opened macro-enabled Excel spreadsheets from external suppliers
- User Application Hardening: No browser hardening policies. Internet Explorer was still installed on four workstations despite Microsoft’s deprecation. No web content filtering in place
- Restrict Administrative Privileges: Every one of the 85 users had local administrator rights on their workstations. Six accounts had Domain Admin privileges — only two of which were legitimately required
- Patch Operating Systems: Four servers were running Windows Server 2012 R2 — end of extended support since October 2023. Twelve workstations were running Windows 10 with automatic updates disabled
- Multi-Factor Authentication: MFA was not enabled for any Microsoft 365 accounts despite all staff accessing email and SharePoint from outside the office. No Conditional Access policies were configured
- Regular Backups: An on-premises backup server was in place, but it was on the same network segment as production systems. The last documented restoration test was over 18 months ago. Microsoft 365 data (email, SharePoint, Teams) had no third-party backup
The 12-Week Implementation Programme
CodeHyper designed and implemented a phased 12-week Essential Eight uplift programme targeting Maturity Level Two across all eight controls.
- Weeks 1–2 | Identity and Access Foundation. Deployed MFA for all 85 users through Microsoft Entra ID with Conditional Access policies. Removed local administrator rights from all standard users. Identified and deprovisioned four excess Domain Admin accounts. Deployed Entra ID Privileged Identity Management (PIM) for the two legitimate administrators requiring elevated access
- Weeks 2–4 | Patching and OS Currency. Deployed Microsoft Intune for centralised patch management and policy enforcement. Established automated patching with a 14-day maximum patch window for applications and 48-hour window for critical vulnerabilities. Migrated the two remaining Windows Server 2012 R2 servers to Windows Server 2022 (third and fourth servers were decommissioned as workloads were consolidated). Upgraded all Windows 10 workstations to Windows 11
- Weeks 3–5 | Application Control and Browser Hardening. Deployed Windows Defender Application Control (WDAC) via Intune in audit mode for two weeks, then enforcement mode. Implemented Microsoft’s recommended application blocklist. Configured browser hardening policies including advertisement blocking, Java disabled in browsers, and blocked high-risk content categories. Restricted PowerShell execution policy
- Weeks 4–6 | Macro Controls. Deployed Microsoft 365 macro policy via Intune restricting macros to digitally signed content from trusted publishers. Worked with operations team to identify two legitimate macro-dependent workflows, converted both to Power Automate flows eliminating the macro dependency. All other users had macros disabled
- Weeks 6–10 | Backup Remediation. Deployed Datto SaaS Protection for Microsoft 365 backup covering Exchange Online, SharePoint, OneDrive, and Teams. Reconfigured on-premises backup solution with network isolation — backup server moved to dedicated VLAN with no outbound internet access and no connection to user workstations. Established quarterly documented restoration testing schedule. Conducted first restoration test to verify RTO/RPO targets
- Weeks 10–12 | Logging, Monitoring, and Validation. Deployed Microsoft Defender for Business with centralised logging. Configured security event alerts for privileged access changes, MFA failures, and application control block events. Conducted internal Essential Eight maturity assessment against ASD’s assessment guidance. Documented all controls for insurance submission
The Results
Outcomes at Week 12 Essential Eight Maturity Level: 0 → Level 2 across all 8 controls | Cyber insurance: Policy renewed at same premium tier with improved coverage terms | Local admin rights removed: 85/85 users | MFA enabled: 85/85 users (100% coverage) | Unpatched critical vulnerabilities: 7 → 0 | End-of-life OS instances: 4 servers + 12 workstations → 0 | Microsoft 365 backup coverage: 0% → 100% | Time to complete: 12 weeks | Disruption to operations: Minimal — no unplanned downtime |
Beyond the insurance renewal, the business experienced an unexpected operational benefit: the removal of local admin rights and the deployment of Intune-managed application control virtually eliminated the IT contractor’s reactive support load from end-user-installed software issues — reducing ad hoc IT support calls by approximately 60% in the first month post-implementation.
“We thought Essential Eight compliance would be a massive, disruptive project. It wasn’t. CodeHyper ran it methodically alongside normal operations, and the biggest impact we noticed initially was actually the support tickets going down — not the security improvements, which we couldn’t see directly. The insurance renewal was the goal, but the outcome was a genuinely better-run IT environment.” — Operations Manager, Melbourne Construction Firm
How to Get Started: Your Essential Eight Implementation Roadmap
Achieving Essential Eight compliance doesn’t require a big-bang transformation. The most successful implementations follow a structured, risk-based approach that builds maturity progressively across all eight controls.
Step 1: Conduct a Gap Assessment
Before you can plan an uplift programme, you need to understand your current maturity level against each of the eight controls. A gap assessment compares your current-state configuration against ASD’s maturity model requirements, identifies your lowest-performing controls, and quantifies the risk exposure associated with each gap. ASD’s Essential Eight Maturity Verification Tool (E8MVT) is a free tool available through the ASD Partner Portal that automates testing of five of the eight controls on Windows systems. Our Essential Eight checklist provides a practical starting point for self-assessment.
Step 2: Set a Target Maturity Level
Not every organisation needs to target Maturity Level Three. ASD’s guidance is clear: set a target maturity level appropriate to your threat environment and implement all eight controls to that level before advancing. For most Australian SMBs, Maturity Level Two is the appropriate target — it provides strong protection against the vast majority of adversaries Australian businesses face while being achievable without enterprise-scale investment.
Step 3: Implement Controls Horizontally, Not Vertically
A critical implementation principle: achieve the same maturity level across all eight controls before advancing any single control to a higher level. An environment with Maturity Level Three MFA but Maturity Level 0 Application Control is not a Level Three environment — it’s a Level Zero environment with an expensive MFA deployment. Attackers will exploit the weakest control.
Step 4: Automate and Verify
Manual processes are not sustainable for Essential Eight compliance at Maturity Level Two and above. Patching, policy enforcement, backup monitoring, and security event logging all require automation to be reliable at scale. Tools like Microsoft Intune, Microsoft Entra ID, Microsoft Defender for Business, and a managed backup solution form the core technology stack for Essential Eight compliance in a Microsoft 365 environment.
Step 5: Test, Document, and Maintain
Compliance is not a point-in-time event. Controls degrade as environments change — new software is installed, new users join, configurations drift. Quarterly reviews, annual maturity assessments, and documented restoration tests ensure your compliance position is maintained. ASD recommends a comprehensive maturity assessment every 12 months and following any significant change to the environment.
Essential Eight Tools: What You Need to Implement Each Control
Essential Eight Control | Recommended Tools for Australian SMBs |
Application Control | Microsoft Intune + Windows Defender Application Control (WDAC), AppLocker (legacy environments) |
Patch Applications | Microsoft Intune, Windows Update for Business, N-able, Automox, Datto RMM |
Configure Macro Settings | Microsoft Intune + Microsoft 365 Group Policy / Admin Centre macro policies |
User Application Hardening | Microsoft Intune browser policies, Microsoft Edge security baselines, web content filtering via DNS |
Restrict Administrative Privileges | Microsoft Entra ID PIM (Privileged Identity Management), Azure AD Conditional Access, Intune compliance policies |
Patch Operating Systems | Microsoft Intune, Windows Update for Business, WSUS (legacy), automated patching via RMM |
Multi-Factor Authentication | Microsoft Entra ID (Conditional Access + MFA), FIDO2 security keys (YubiKey, Feitian) for phishing-resistant MFA |
Regular Backups | Datto SaaS Protection (Microsoft 365), Veeam, Azure Backup, Acronis — combined with offline/immutable storage |
Don’t Wait for a Breach to Take the ASD Essential Eight Seriously
The ASD Essential Eight exists because Australia’s national cybersecurity agency has seen — repeatedly, across thousands of incidents — that a small set of well-implemented controls prevents the majority of attacks. The framework is not theoretical. It is built from real-world incident response data, real attacker techniques, and real breach outcomes.
In 2026, the question for Australian businesses is not whether to implement the Essential Eight — it’s how quickly you can close your gaps before your insurer, your clients, or an attacker forces the issue.
At CodeHyper, we deliver Essential Eight gap assessments and maturity uplift programmes for Australian SMBs — designed to achieve measurable, documentable compliance efficiently and without disrupting your operations. We also provide ongoing managed cybersecurity services that maintain your Essential Eight maturity as your environment evolves.
Start with our Essential Eight checklist for 2025 to self-assess your current maturity. Or contact us today for a professional gap assessment — and let’s close the gaps before they become headlines.
Frequently Asked Questions: ASD Essential Eight
What is the ASD Essential Eight?
The ASD Essential Eight is a set of eight prioritised cybersecurity mitigation strategies developed by the Australian Signals Directorate (ASD) through the Australian Cyber Security Centre (ACSC). Published in 2017 and updated regularly, it represents the minimum security baseline ASD recommends for all Australian organisations with internet-connected IT systems. The eight controls address the most commonly exploited weaknesses and are designed to prevent, limit, and recover from cyberattacks.
Is the ASD Essential Eight mandatory for Australian businesses?
The Essential Eight is mandatory for all non-corporate Commonwealth entities (NCCEs) under the Protective Security Policy Framework (PSPF). For private sector businesses, it is strongly recommended but not legislatively mandated — however, practical enforcement is increasing through cyber insurance requirements, government procurement conditions, and contractual obligations from clients operating in regulated sectors. In 2026, businesses that cannot demonstrate Essential Eight compliance face real commercial consequences even without a direct legal mandate.
What are the four Essential Eight maturity levels?
The Essential Eight Maturity Model defines four levels: Level 0 (minimal or no controls implemented), Level 1 (basic protection against opportunistic attacks using commodity tools), Level 2 (intermediate protection against adversaries with moderate resources and standard tradecraft — the expected baseline for most Australian businesses), and Level 3 (advanced protection against sophisticated adversaries with significant resources, targeted techniques, and persistence).
What is the difference between Maturity Level 1 and Level 2?
Maturity Level One addresses opportunistic, automated attacks and allows manual processes. Maturity Level Two addresses adversaries investing significant effort against specifically targeted organisations and requires more comprehensive implementation, automated patching, phishing-resistant MFA for privileged accounts, centralised logging, and stronger backup isolation. For most Australian businesses holding customer data, Level Two is the appropriate target — Level One provides insufficient protection against the adversaries currently targeting Australian organisations.
How long does it take to implement the ASD Essential Eight?
For a typical Australian SMB running Microsoft 365 with 50–150 staff, achieving Maturity Level Two across all eight controls takes approximately 8–16 weeks depending on the starting maturity, complexity of the environment, and internal IT capacity. The Melbourne construction business case study in this article achieved Level Two in 12 weeks with CodeHyper’s support. Larger or more complex environments may take longer, but the process is manageable and does not require significant operational disruption when planned properly.
What is phishing-resistant MFA and why is it required at Level 2?
Phishing-resistant MFA refers to authentication methods that cannot be intercepted or replicated through phishing attacks. Standard SMS OTPs and authenticator app TOTP codes can be stolen by real-time phishing proxy tools that intercept the authentication session. Phishing-resistant MFA — specifically FIDO2 hardware security keys (like YubiKey) or certificate-based authentication — binds the authentication to a specific registered device and domain, making interception technically impossible. ASD requires this for privileged users from Maturity Level Two because privileged accounts are the highest-value targets for sophisticated attackers.
Does the Essential Eight cover cloud environments like Microsoft 365?
Yes, though the original framework was designed for on-premises Windows environments, ASD and Microsoft have both published detailed guidance on implementing Essential Eight controls in Microsoft 365 and Azure environments. Microsoft Intune, Microsoft Entra ID (Conditional Access and PIM), Microsoft Defender for Business, and services like Datto SaaS Protection for Microsoft 365 backup form the core implementation stack for cloud-based Essential Eight compliance. ASD’s Small Business Cloud Security Guides specifically address Microsoft 365 hardening to Essential Eight Maturity Level One.
How does the Essential Eight relate to the Privacy Act and data breach notification?
The Essential Eight and the Privacy Act 1988 (including the Notifiable Data Breaches scheme) are complementary. Implementing the Essential Eight significantly reduces the risk of a data breach notifiable under the Privacy Act — because most breaches result from the exact vulnerabilities the Essential Eight controls address. Organisations that suffer a data breach and cannot demonstrate reasonable security measures face greater regulatory scrutiny and potential enforcement action. Essential Eight compliance provides documented evidence of reasonable security practices.
What is the Essential Eight Assessment Process Guide?
The Essential Eight Assessment Process Guide is an official ASD publication that provides detailed, step-by-step methods for testing the implementation of each Essential Eight control. It is used by both organisations conducting self-assessments and external assessors evaluating an organisation’s maturity. ASD has also released the Essential Eight Maturity Verification Tool (E8MVT) — a free automated testing tool available through the ASD Partner Portal — that assesses five of the eight controls on Windows systems.
How do I get an Essential Eight assessment for my Australian business?
A professional Essential Eight gap assessment involves a structured review of your environment against ASD’s current maturity model requirements, producing a maturity rating for each of the eight controls and a prioritised remediation roadmap. CodeHyper conducts Essential Eight assessments for Australian businesses as a standalone engagement or as the first phase of a managed cybersecurity engagement. Contact us today to discuss your requirements and what a gap assessment would involve for your specific environment.