If you’re running a growing business in Sydney, you’ve likely heard the terms NOC and SOC thrown around during IT discussions. They sound similar. They both involve monitoring. And they both claim to protect your business.
But they solve very different problems.
Understanding the difference between a Network Operations Center (NOC) and a Security Operations Center (SOC) isn’t just technical trivia. It directly impacts your uptime, security posture, compliance position, and risk exposure.
For SMEs especially, choosing the wrong operational model can mean wasted budget — or worse — missed cyber threats.
Let’s break it down properly.
What Is a NOC?
A Network Operations Center (NOC) is responsible for monitoring, maintaining, and optimising your IT infrastructure to ensure systems remain operational.
Think uptime. Stability. Performance.
A NOC monitors:
- Servers
- Network devices (switches, routers, firewalls)
- Cloud infrastructure
- Internet connectivity
- Backup systems
- Hardware health
If your internet drops, your server overheats, or your cloud environment misconfigures — the NOC handles it.
For businesses using managed IT providers, NOC services are often part of broader support agreements like your Managed IT Services Sydney Buyer’s Guide framework.
The NOC focuses on availability and performance, not active threat hunting.
What Is a SOC?
A Security Operations Center (SOC) is responsible for detecting, investigating, and responding to cyber threats.
Think protection. Threat intelligence. Incident response.
A SOC monitors:
- Suspicious login attempts
- Malware behavior
- Ransomware activity
- Data exfiltration
- Phishing campaigns
- Endpoint anomalies
SOC teams analyse security alerts generated from tools like EDR, SIEM, firewall logs, and identity systems.
If you’ve read about Building a Security Operations Center, you’ll know that a SOC is structured around continuous threat monitoring, rapid containment, and forensic investigation.
In short:
- NOC = Keeps systems running
- SOC = Stops attackers from breaking in
Different missions. Different skill sets.
NOC vs SOC: 5 Key Differences

Here’s where most business owners get confused. Monitoring is not the same as security monitoring.
1. Primary Objective
NOC ensures uptime.
SOC ensures security.
2. Alert Type
NOC handles performance alerts (CPU spikes, outages).
SOC handles threat alerts (malware, suspicious behaviour).
3. Tools Used
NOC relies on RMM platforms, infrastructure monitoring tools, and network dashboards.
SOC relies heavily on EDR, SIEM platforms, and threat intelligence feeds.
4. Skill Sets
NOC engineers specialise in networking, cloud systems, infrastructure optimisation — similar to topics covered in IT Infrastructure Optimisation.
SOC analysts specialise in cybersecurity frameworks, MITRE ATT&CK (see Understanding TTPs), digital forensics, and incident response.
5. Business Impact
NOC prevents downtime.
SOC prevents breaches.
One protects productivity. The other protects reputation and compliance.
Why Sydney SMEs Often Need Both
Modern IT environments are hybrid:
- Microsoft 365
- Cloud storage
- On-prem systems
- Remote employees
- SaaS platforms
If you’re using cloud platforms, you’re already exposed to identity-based threats. That’s where solutions like Entra ID become critical from a SOC perspective.
At the same time, you need stable backups and disaster recovery — areas tied closely to Cloud Backup Strategy and Disaster Recovery Plan Checklist.
A NOC ensures these systems stay operational.
A SOC ensures they stay secure.
SOC vs NOC: Which One Is Better?
This is the wrong question.
It’s like asking whether brakes are better than headlights.
If your business only cares about uptime but ignores cybersecurity, you’re vulnerable. If you invest only in threat detection but ignore infrastructure health, your operations suffer.
The better question is: What risk profile does your business have?
If you operate in regulated industries or handle sensitive client data, SOC becomes non-negotiable. Frameworks like the NIST Framework highlight the need for detection and response capabilities — not just availability monitoring.
How SOC and NOC Work Together
In mature environments, NOC and SOC integrate.
For example:
- NOC detects abnormal server behaviour
- SOC determines whether it’s hardware failure or malware
- NOC restores services
- SOC investigates root cause
If ransomware strikes:
- SOC isolates infected endpoints (see Responding to Alerts in EDR)
- NOC ensures backups are intact via services like BCDR
- Business operations resume quickly
That synergy is what modern managed providers aim to deliver.
Skill Sets: SOC vs NOC Career Paths
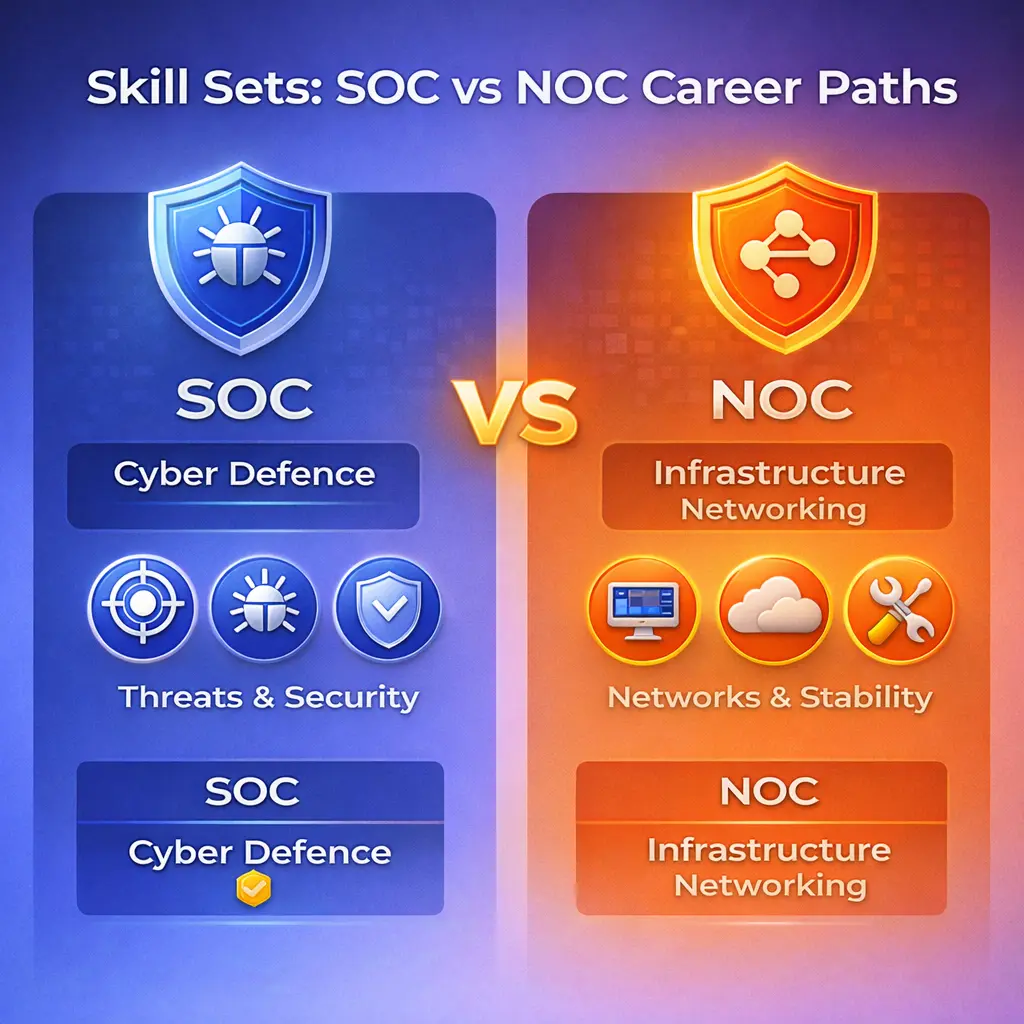
For those exploring IT careers:
NOC roles focus on:
- Networking fundamentals
- Cloud deployment
- Infrastructure management
- Troubleshooting
SOC roles focus on:
- Threat hunting
- Malware analysis
- Incident response
- Security frameworks
- Penetration testing knowledge
If your interest is infrastructure stability, networking is strong.
If your interest is cyber defence, SOC roles are in higher long-term demand — especially with the rise of AI-powered attacks (see AI in Cybersecurity).
What Happens If You Only Have a NOC?
You might detect a system slowdown.
But you won’t detect a silent data breach.
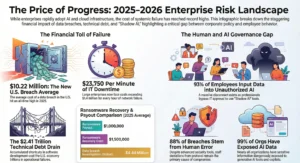
Many breaches go unnoticed for months. Without SOC-level monitoring, malicious actors can:
- Move laterally
- Escalate privileges
- Extract sensitive data
Sydney businesses increasingly face sophisticated phishing and impersonation attacks (see Email Spoofing Prevention).
A NOC alone does not handle these threats.
What Happens If You Only Have a SOC?
You may detect threats.
But poor infrastructure management can still cause downtime.
If your cloud migration isn’t optimised, or your backups are misconfigured, even the best SOC cannot fix availability problems.
That’s where integrated service models matter.
When Should SMEs Invest in SOC?
SOC becomes critical when:
- You handle financial data
- You operate in healthcare, legal, or government sectors
- You rely heavily on Microsoft 365
- You have remote employees
- You want 24/7 threat monitoring
Cybersecurity is no longer optional. Articles like Cyber Threat Landscape for Australian SMBs highlight how attack frequency is increasing year over year.
Cost Considerations: NOC vs SOC
NOC services are generally included within broader managed IT packages.
SOC services, particularly 24/7 monitoring, require:
- Advanced tooling (EDR, SIEM)
- Skilled analysts
- Continuous threat intelligence
That’s why many businesses outsource SOC through managed cyber security services.
For SMEs, outsourcing provides enterprise-level security without enterprise-level payroll costs.
Do You Need a Full SOC?
Not necessarily.
Many Sydney SMEs adopt a hybrid approach:
- Managed IT (NOC) for uptime
- Managed SOC monitoring for cybersecurity
- Periodic vulnerability scanning
- Regular penetration testing
This layered model reduces risk significantly.
Final Verdict: NOC vs SOC for Sydney Businesses
If your goal is operational stability, you need a NOC.
If your goal is cyber resilience, you need a SOC.
If your goal is long-term business protection — you need both working together.
Technology complexity is increasing. Attack sophistication is rising. Regulatory expectations are tightening.
The businesses that survive and scale are the ones that treat uptime and security as two sides of the same coin.
FAQs
Which one is better NOC or SOC?
Neither is better; NOC protects uptime while SOC protects against cyber threats, and most businesses need both.
What is best for a future job, IT security or networking?
Cybersecurity roles in SOC environments are growing faster due to rising threats, but networking remains foundational for infrastructure careers.
What does a network security specialist do on a daily basis?
They monitor systems, analyse alerts, investigate suspicious activity, implement security controls, and respond to cyber incidents.