Cybersecurity has evolved rapidly over the past decade.
Traditional antivirus became obsolete.
EDR emerged as the new standard.
Now XDR is taking centre stage.
But this is not just another acronym battle.
The shift from Endpoint Detection and Response (EDR) to Extended Detection and Response (XDR) reflects how cyber threats have changed — and how businesses must respond.
If your organisation is evaluating XDR vs EDR, this guide will break down:
- Core differences
- Detection capabilities
- Architecture impact
- Cost considerations
- Use-case scenarios
- Security maturity alignment
Let’s go deep.
What Is EDR (Endpoint Detection and Response)?
EDR focuses specifically on endpoints, including:
- Laptops
- Desktops
- Servers
- Workstations
- Mobile devices
Instead of relying on signature-based antivirus scanning, EDR continuously monitors endpoint activity and detects suspicious behaviour such as:
- Privilege escalation
- Unusual file execution
- Lateral movement
- Ransomware encryption patterns
- Command-and-control communication
EDR provides:
- Real-time monitoring
- Threat detection
- Forensic investigation tools
- Automated containment capabilities
For many organisations, EDR was a massive improvement over traditional antivirus.
If you’re exploring endpoint protection in more depth, see our dedicated EDR solution page.
What Is XDR (Extended Detection and Response)?
XDR expands detection beyond endpoints.
It aggregates and correlates security data from multiple environments, including:
- Endpoints
- Email systems
- Cloud applications
- Identity and access management platforms
- Network traffic
- SaaS environments
- Servers
Rather than investigating a single device, XDR connects activity across the entire IT ecosystem.
This matters because modern cyberattacks are multi-stage and multi-layered.
Example:
- A phishing email bypasses spam filters.
- Credentials are harvested.
- An unusual login occurs from another country.
- Files are accessed in cloud storage.
- Data exfiltration begins.
EDR may detect suspicious activity on the device.
XDR sees the full attack chain across email, identity, cloud, and endpoint systems.
That context dramatically improves detection speed and response precision.
XDR vs EDR: Core Differences
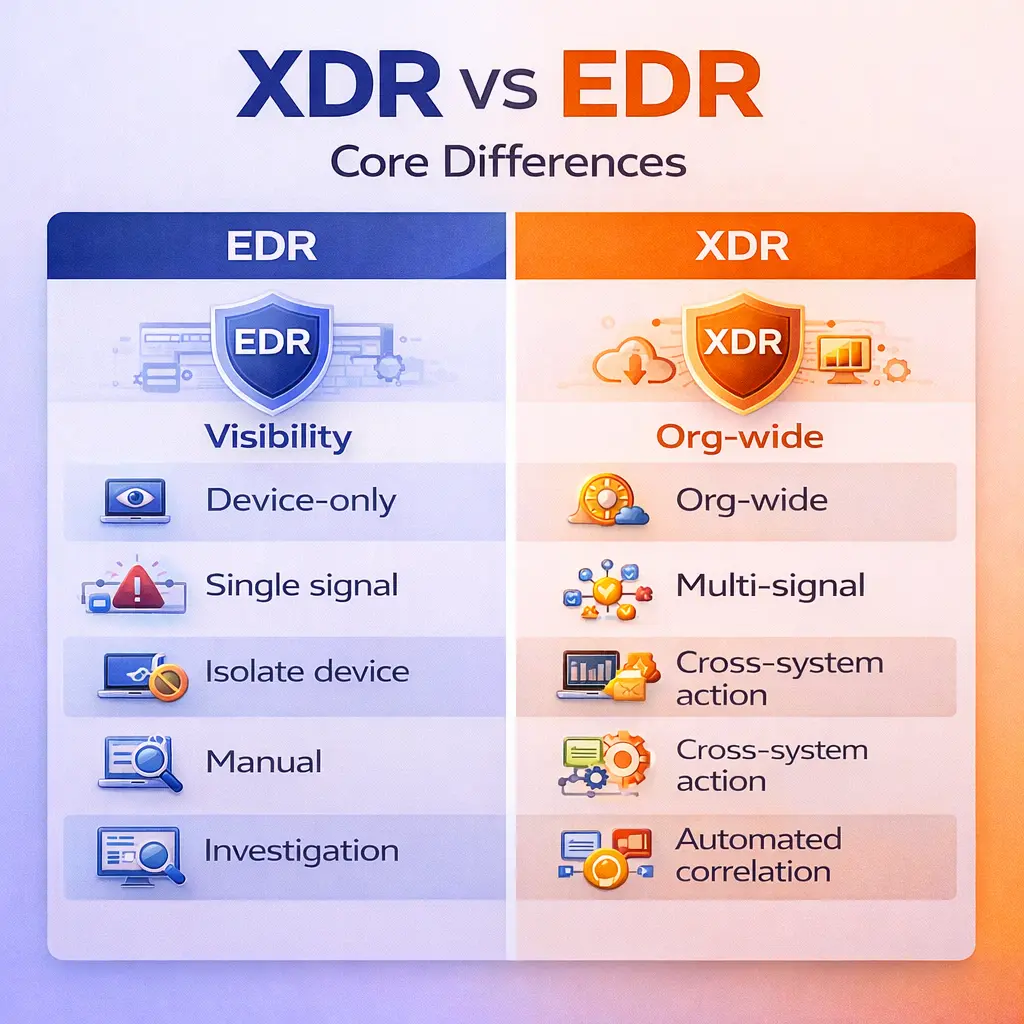
1️⃣ Scope of Visibility
EDR = Endpoint-only visibility
XDR = Cross-platform, environment-wide visibility
EDR monitors individual devices.
XDR correlates signals across the organisation.
2️⃣ Detection Accuracy
Because XDR correlates multiple signals, it reduces false positives.
For example:
A login from a new location alone might not trigger a high-risk alert.
But combine that with:
- Email phishing activity
- Suspicious endpoint behaviour
- Abnormal cloud file access
Now the pattern becomes obvious.
Correlation is the power shift.
3️⃣ Response Capabilities
EDR can:
- Isolate a device
- Kill malicious processes
- Roll back ransomware changes
XDR can:
- Disable compromised accounts
- Block malicious IPs
- Contain endpoints
- Suspend suspicious cloud sessions
- Enforce identity-based restrictions
It operates across systems, not just devices.
4️⃣ Security Operations Efficiency
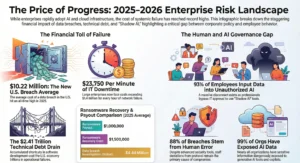
According to IBM, reducing detection and response time significantly lowers breach costs.
You can explore breach cost research here.
XDR improves detection time because it reduces manual log analysis across siloed tools.
EDR requires more manual investigation.
Why XDR vs EDR Matters in 2026
Threat actors no longer rely on malware alone.
Modern threats include:
- Credential abuse
- Business email compromise
- Cloud misconfiguration exploitation
- API abuse
- Supply chain infiltration
- AI-assisted phishing campaigns
These attacks span multiple systems.
If your security visibility is limited to endpoints, you are analysing fragments of a larger event.
The modern attack surface is distributed.
Security visibility must match that reality.
For additional industry threat intelligence insights, see resources from CISA.
When Is EDR Enough?
EDR may be sufficient when:
- The organisation has a small infrastructure footprint
- Limited SaaS usage
- Minimal cloud adoption
- Strong internal security monitoring
However, EDR alone creates blind spots if:
- Microsoft 365 is heavily used
- Staff work remotely
- Cloud applications store sensitive data
- Identity management is complex
EDR without continuous monitoring also creates a false sense of security.
Detection tools are only as strong as the response capability behind them.
When Is XDR the Smarter Investment?
XDR becomes strategic when:
- The organisation uses hybrid cloud infrastructure
- Remote or hybrid workforce models exist
- Regulatory or compliance requirements are strict
- Business continuity is critical
- There is limited in-house SOC capability
XDR consolidates tools and improves signal-to-noise ratio, reducing alert fatigue.
It moves security posture from reactive to proactive.
XDR vs EDR: Cost Comparison
EDR appears cheaper initially.
But cost evaluation must include:
- Breach recovery expenses
- Downtime impact
- Regulatory penalties
- Ransomware payments
- Data restoration costs
- Reputation damage
If your environment is complex but your detection scope is narrow, you are under-protected.
In cybersecurity, cost savings at the detection layer often create exponential risk at the breach layer.
Does XDR Replace EDR?
No.
XDR includes endpoint detection capabilities as part of its broader framework.
Think of EDR as one component within the XDR architecture.
XDR builds on EDR.
It does not eliminate it.
The Human Layer Still Determines Outcomes
Regardless of EDR or XDR deployment, most breaches begin with:
- Phishing
- Social engineering
- Poor credential discipline
- Excessive privileges
Technology cannot compensate for untrained users.
Continuous cybersecurity awareness and structured governance are essential.
Security is layered.
Detection is one layer.
Training is another.
Governance is the framework that binds them.
Choosing the Right Path for Your Business
The decision between XDR vs EDR depends on:
- Infrastructure complexity
- Risk tolerance
- Regulatory exposure
- Cloud adoption
- Internal security expertise
For many growing organisations, EDR was sufficient five years ago.
In 2026, most environments have expanded beyond endpoint-only risk.
The attack surface is now identity-driven and cloud-connected.
Detection must reflect that expansion.
If you’re unsure where your security posture stands, explore our cybersecurity solutions.
Or speak directly with our team to assess your environment:
Final Position
EDR was a major advancement over traditional antivirus.
XDR reflects the modern threat landscape.
The real question in the XDR vs EDR debate is not about acronyms.
It is about visibility.
If your organisation has expanded its infrastructure, cloud presence, and remote workforce — but your detection remains endpoint-focused — you have a visibility gap.
Cybersecurity maturity is not defined by tools.
It is defined by the elimination of blind spots.
FAQs
What is the main difference between XDR and EDR?
EDR monitors and responds to threats at the device level. XDR extends visibility across endpoints, email, identity systems, cloud platforms, and networks, correlating events across the entire environment.
Is XDR better than EDR for businesses?
For organisations with cloud infrastructure, hybrid workforces, or complex IT environments, XDR provides broader visibility and stronger threat correlation. Simpler environments may still benefit from EDR.
Does XDR cost more than EDR?
XDR often has a higher upfront investment but reduces operational risk, false positives, and breach impact. Long-term cost must include breach exposure and downtime risk.
Can small businesses use XDR?
Yes. Many XDR solutions are scalable and cloud-based, making them accessible for small and mid-sized businesses seeking proactive threat detection.
Should EDR be replaced immediately?
Not necessarily. The decision depends on infrastructure complexity and risk exposure. However, businesses with expanding cloud and identity layers should evaluate XDR seriously.